If you were to ask the ordinary individual to define the Internet, they could mention the browser they use to get online, the search engines they employ, discussion boards like Reddit, and their preferred news, entertainment, and social media sites.
The term “surface web” is used to describe this subset of the entire Internet. Regular web browsers like Safari and Chrome can access this part of the internet, and public search engines like Google and Bing have indexed and made it searchable.
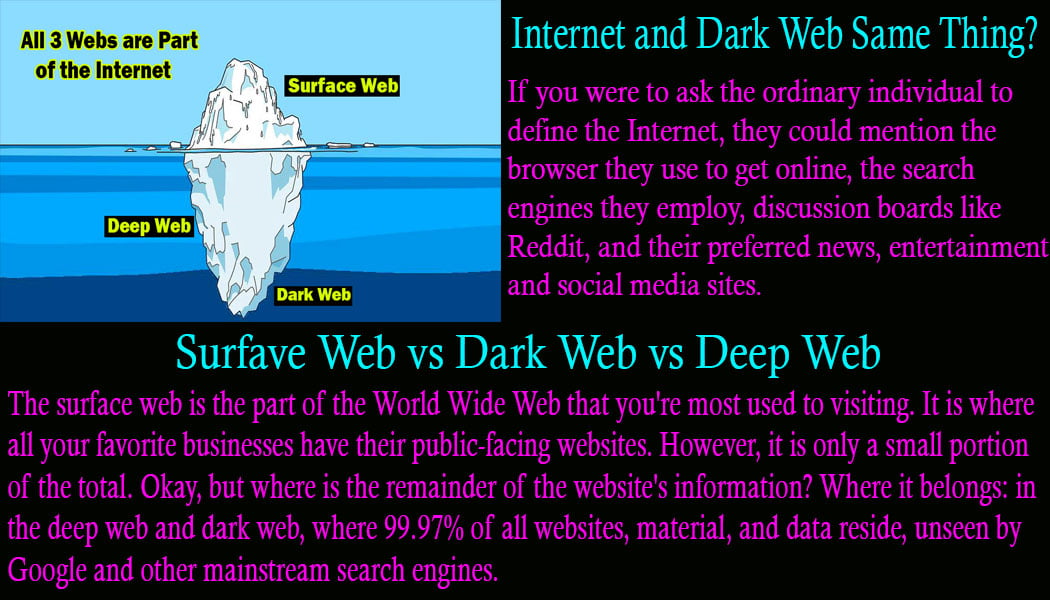
The surface web is part of the World Wide Web that you’re most used to visiting. It is where all your favorite businesses have their public-facing websites. However, it is only a small portion of the total.
Okay, but where is the remainder of the website’s information? Where it belongs: in the deep web and dark web, where all websites, material, and data reside, unseen by Google and other mainstream search engines.
This article will discuss how darknet and deep web resources differ, how to identify and combat cyber dangers emanating from them, and what sorts of information and resources they offer.
How do we tell the Difference Between the Deep Web and the Regular Internet?
The primary distinction is that indexed search results may be found on the “surface web,” while those on the “dark web” cannot. However, you can still get to it. The term “dark web” now refers to a subset of the Internet consisting of resources. That is inaccessible without using “overlay networks,” which operate invisibly on top of the regular Internet. Since much of the Dark Web is encrypted and most darknet pages are hosted anonymously, you will need special software in order to access it.
Different methods exist for accessing various areas of the web. When it comes to gaining entry to the darknet, TOR (The Onion Router) remains the most often used software. The anonymous Tor browser is their bread and butter. However, if you believe you are fully anonymous, you can be mistaken. Authorities frequently remove and prosecute Dark Web sites and users who engage in criminal activity.
Internet traffic on the Tor network is routed through a distributed system of anonymous relays. Browsers create a chain of secure connections one at a time. Because each relay only knows the two relays before and after it, the whole communication route remains almost impossible to trace. An onion analogy can be made between the several layers of encryption.
What can you find on the Dark Web?
There is a strict requirement for anonymity when visiting dark web links; thus, users may only access it with a special browser like Tor that encrypts all web traffic. Due to its anonymity, the dark web has become a sanctuary for criminals of all stripes, from petty thieves to international cartels.
Oftentimes, personally identifiable information (PII) and other types of sensitive data taken from business targets are sold on the darknet.
The resources on darknet links are not only inaccessible without the use of special software, but they are also not visible in standard web searches. That’s why it makes sense to classify the darknet with other software-gated websites: as a subset of the regular web.
Bitcoin is a common form of payment among dark web criminals. The secrecy and ease of use of bitcoin have made it the de facto digital currency for online drug sales and money laundering.
On the darknet, fraudsters can buy and sell stolen passwords to email accounts and bank accounts, as well as share knowledge and resources with one another.
Can you Access the Dark or Deep Web Without any Legal Consequences?
It should be obvious from our explanation of the deep web that many parts of it are perfectly legal to access. Including your inbox, the files in your Dropbox account, your company’s Intranet, and private websites to which you have been granted access.
It is still against the law to use deceptive means to access someone else’s personal data or deep web resources. (e.g., hacking into the corporate intranet or public cloud of a rival company, executing an email account takeover attack, etc.).
The use of Tor and other darknet browsers is perfectly legal in the US. However, there are always legal repercussions for illegal actions taken by individuals on the internet. Such as buying narcotics, viewing content that has been restricted, or committing fraud.
How can you Safely Visit the Dark Web?
Even if you’re just going to dark web links to look at your dental bill or bank account balance, you should have reliable security software installed and updated on your computer.
Use a virtual private network (VPN) while going to dark web links and using your online credit card portal. A VPN can shield your online activity by masking your IP address and encrypting any data you send or receive. This prevents your online communications and activity from being monitored by the government, advertisers, and hackers. Your online banking password will be safe from hackers and other potential security risks.
Tips to Access the Dark Deb Safely
Tor’s anonymizing features make it a useful tool for communicating privately with loved ones or reporting wrongdoing through dark web links. Always use the most recent versions of Tor and Tor client software. The software running your gadget should also be up to date. Never use your usual email address on a webpage when using Tor. Although Tor is intended to protect your anonymity, using a conventional email account could be a security risk.
Some people’s “character” on the dark web may be in doubt due to their participation in unlawful activities. So, it’s crucial that you take precautions to safeguard your privacy and identity.
Going to dark web links, however, is not the same as going to the deep web. In fact, exploring the dark web is a surefire way to get into some kind of legal problems. Contrasted with the deep web, which houses valuable resources, the dark web is a cesspool of immorality.
Why is Tor the Best Option to Access the Dark Web?
There is no way to monitor or restrict the information, goods, and services offered. Since Tor servers protect the privacy of both users and authors on dark web links. Payments are sent and received in Bitcoin, the digital money that is decentralized and hence impossible to track.
It’s a common misconception that only criminals use dark web links. There are newspapers whose editors and founders consider the dark web to be their sole option for achieving and maintaining a truly free press.
Do your research on the risks involved in exploring dark web links before venturing there. To protect your information and identity online, it is important to have a reliable, up-to-date security suite installed and running on all of your devices.
Should a Common Internet User Visit the Dark or Deep Web?
You most likely are already a frequent visitor to the deep web. You have been on the deep web if you have ever viewed your bank or credit card statements online or checked your online account balance. When you log into Netflix, Amazon Prime, or any streaming video provider, you are using the deep web.
What is this, the shadowy depths of the Internet? Then we’re talking about a separate issue. If your government restricts or monitors your internet activities, you may wish to use the dark web. You can access sites that your government doesn’t want you to see by using the Tor browser to access the dark web.
If you are a dissident who wants to avoid government snooping on your communications, dark web links may be the way to go. Perhaps you work in the media and are communicating with anonymous sources. The deep web is a useful tool.
Dark web websites have even become a forum for doctors to discuss private patient information. Having this option means that people can feel safe asking inquiries about sensitive health topics.
Caution is advised when navigating the deep web. You can find everything from narcotics to firearms to child pornography on this area of the web. It’s also a marketplace where hackers sell sensitive information about their victims. Such as their credit card data and Social Security numbers. Remember that this may come back to haunt you.
Conclusion
The dark web is distinct from the regular Internet. To access the dark web, users must first switch to a special browser. That connects them to private, encrypted networks instead than the public ones often used for regular web browsing.

